BugForge Write-Up 3/13/2026
- icanhaspii
- Mar 14
- 4 min read
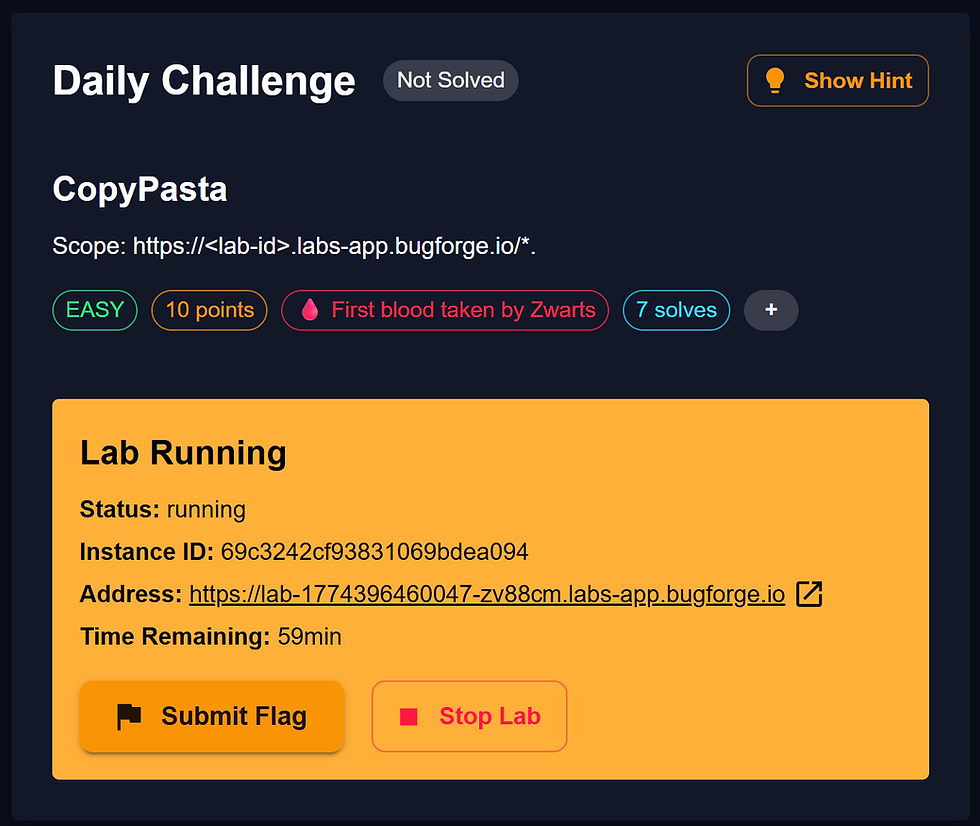
BugForge Daily Challenge 3/13/2026 - Gift Lab

Hint: Can you craft a token?

Author’s Note:
I followed along with the @_shadowforge__ write-up to solve this one. It was a privilege to read a write-up from the author of the challenge themself! I will say, that even though I solved the challenge (which was a triumph I felt great about, because it was only due to what I’ve learned thus far doing these daily BugForge challenges), afterward I was feeling like I wasn’t 100% sure of exactly what was going on behind the curtain of this Web app, and what precisely I’d just exploited, and how. So, after seeing a couple questions over in the Discord channel for this challenge, I decided to publish my quite unwieldy notes for this one...so bear with me please, I tried to clean them up so others could learn as I had, but they are pretty rough, and some of the screen grabs might be a bit off. Alright, as my manager at work likes to say (former Navy pilot), “Let’s move out!”
Note:
If there is an admin account active for a lab, the credentials are admin:admin123
I launched Caido.
I checked to see if there was an admin login using the set/known creds, but there was not.
Next, I created a new user account, and once logged in, the platform behaved a lot like a to-do list site, so I poked around a bit, trying to see everything I could do with the app and generating some traffic to view via the proxy.
So, re-reading the @_shadowforge__ write-up after solving this, I wanted to go back and dig a bit deeper into what had just happened. First, we look at our login traffic via our proxy interceptor, and we see our login contained an “adminAccessToken”, which led @_shadowforge__ to believe there must be an admin panel.
In an attempt to find the administrator panel, @_shadowforge__ suggested we “FUZZ” the application. It had been some time since I had fuzzed anything, so I thought I’d try to take a shortcut and use the @PawPawHacks/Tom Fieber endpoint finder tool (I wrote about how to use the tool here) but that one did not yield an admin panel (but we knew there was one). I do recall there was a reason given a couple months back about why sometimes that script won’t find everything...something about certain endpoints can be hidden maybe? Don’t quote me on that, it was some time ago and I didn’t take notes on it:
/dashboard
/logout
/lists
/
So, no time saved with that shortcut, in fact, time lost 🙁 LOL! OK, so next up, time to RTM (left out the “F”) 😇. Again with the fuzzing, I was trying to save time so I grabbed a quick wordlist, but after the @ZWarts write-up came out (later) I realized that probably their recommended wordlist, and a much better choice, would have been the one they used: common.txt (FYI, this is a well-known wordlist by the amazing Daniel Miessler who now focuses on AI and pumps out an incredible weekly newsletter which I highly recommend...but, I digress).
One last thing about wordlists, some of them are more tailored to certain tasks (or common words). For example, rockyou.txt (or the newer One Rule) is kind of a “Hail Mary”, if you will...and I believe it’s based more on people’s passwords, but for something like this task, you really want a more custom wordlist made up of common directory/endpoint names used when building Web apps...if that makes sense? You can view the wordlist and command I used below...I did get lucky, and it did find an “administrator” endpoint W00t! I’ll take that as a slow win, LOL!

Alright, so we now have a confirmed target. But, we get “Access Denied” when we try to hit that endpoint...which makes sense, because we aren’t an admin.
So, as a next-step, the author, @_shadowforge__ mentioned running the newfound endpoint via “Sequencer”. I was like, what? What is that? Turns out, after a little bit of Google-Fu, I learned that Sequencer was part of Burp, so I just took a shot in the dark, and hit the orange “Start live capture” button:

What happened next was a bit of a mystery to me, but somehow after running “Sequencer”, by viewing the entropy, we have our next-step. @7s26simon explained it perfectly and eloquently in the BugForge Discord (see his quote below, and if you’re not a member already, come on over)...he also put out a great write-up after I solved the challenge.
In shadow’s writeup he was checking the entropy and seeing what part of the token changes. It’s the proper way to do it. I skipped that step because I could just eyeball the token and see the change after studying each token.
Oooooooh, so that helped. So we know that this thing called a “Cookie Token”, which I’d never heard of (yeah, I know about Cookies, but this was something different), was vulnerable to “cracking” because only the last 3 digits change, I think we see that after running Burp “Sequencer” here:

OK, so the final piece of our puzzle is to brute-force that Cookie Token. @7s26simon wrote a script for that, and @_shadowforge__ used Burp Intruder. Admittedly, this is where I sort of feel like I didn’t really deserve the flag, because I didn’t quite understand what to put into Intruder, and the @7s26simon write-up hadn’t yet been published. So, using Caido “Replay”, I replaced the last 3-digits of my “adminAccessToken” with the “rls” from the @_shadowforge__ write-up, and then saw that when I hit the red “Send” button, that went through:

So from there, I still needed to get the flag over in the Web app. The way I did that was, I “jiggered’ a few things. I went into Chrome’s “Inspect” tool (to get there just hit F12, or right-click in your browser and choose “Inspect”). From there, I went to the “Storage” tab and then hit the drop-down for “Cookies”. After that, I pasted the working “adminAccessToken” (n0MqjBXna9A4rls) and hit the “Enter” key on my keyboard. Then, after a browser refresh, I got the flag!

bug{********************************}
##### End of Report #####