BugForge Write-Up 3/4/2026
- icanhaspii
- Mar 5
- 2 min read
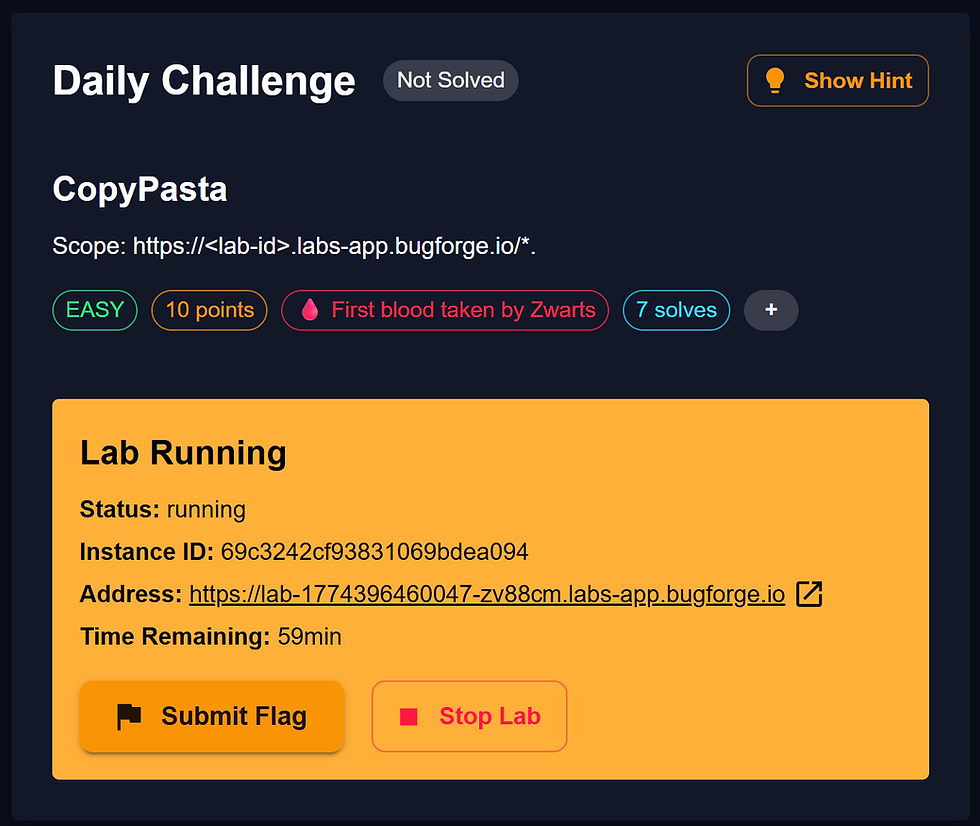
BugForge Daily Challenge 3/4/2026 - CopyPasta

Hint: SQL Injection.

Note:
If there is an admin account active for a lab, the credentials are admin:admin123
I launched Caido.
I checked to see if there was an admin login using the set/known creds, but there was not.
I created a user account and was taken to an app that appeared to behave a lot like PasteBin, so I poked around a bit, trying to see everything I could do with the app and generating some traffic to view via the proxy. I created some "Snippets" (I made one "Public" and one "Private"):

Next, I hit the "View" button on my "Private" Snippet, and then the "Share" button to share-out that Snippet, and I was given the following "Share Link": https://lab-1772678133851-iirgfu.labs-app.bugforge.io/share/b88787b6-3603-4a81-8846-ac12497b4c01:

Following along with the @7s26simon, @__shadowforge__, and @zwarts write-ups, I knew it was important to look at the shared link that gets created by the app and test it for SQL vulnerability. So, over in my Caido proxy window, I found the traffic for the creation of the shared URL: "GET /api/snippets/share/b88787b6-3603-4a81-8846-ac12497b4c01" I'd just created, so I highlighted that line, then right-clicked and selected, "Send to Replay -> Default Collection":

Moving over to the Caido "Replay" tab, I hit the red "Send" button so that I would have a baseline of what the traffic "Response" looked like.
Note: I am skipping the enumeration piece as I ran out of time to write everything up, but other write-ups have documented that piece really well, so be sure to visit those too.
Still following along with the @7s26simon, @__shadowforge__, and @zwarts write-ups, and still in the Caido "Replay" tab, inside the "Request" pane, I made the following change to the first line:
GET /api/snippets/share/b88787b6-3603-4a81-8846-ac12497b4c01'%20and%201=1-- HTTP/1.1
to:
GET /api/snippets/share/b88787b6-3603-4a81-8846-ac12497b4c01'UNION%20SELECT%201%2C1%2CGROUP_CONCAT(username)%2CGROUP_CONCAT(password)%2C1%2C1%20FROM%20users%20-- HTTP/1.1
Note: https://www.eso.org/~ndelmott/url_encode.html seems to help explain URL Encoding, as does the following Google result:

Next, when I hit the red "Send" button, I got the flag:

##### End of Report #####